
A proxy serves as an intermediary between your device and the internet. So it takes your requests, processes it, and then sends it to the web from where the information you need is sent back to you via the proxy. It can be likened to asking a friend to enquire on your behalf. Your friend enquiries, and gets the result back to you. you remain anonymous as no one would know you requested in the first place. There are however different anonymity levels and they depend on the type of proxy you choose.
There are different proxies on the internet, each one being perfect for a specific purpose. The most popular of these is the HTTP proxy and it provides you with great ways to conceal your identity on the internet. HTTP is often used with bots and scrapers and is preferred to SOCKS protocol as it can easily interpret data and is more compatible with the computers.
Post Quick Links
Jump straight to the section of the post you want to read:
Proxies Based on Protocol
1 . HTTP Proxy
An HTTP proxy is one that connects to the target website using HTTP (HyperText Transfer Protocol). Since HTTP is very popular on the internet, it's common to see HTTP proxies in use as they can easily access the web pages you send requests to.
2. HTTPS/SSL Proxy
SSL is short for Secure Socket Layer, and it’s an additional security layer on the HTTP, making it HTTPS. By adding this layer, there are additional security certificates that are available and used for end to end encryption so that all transferred data remains secure. So when inputting username and password on a website with SSL, you can do it with peace of mind.
3. SOCKS Proxy
SOCKS proxies are used to route traffic by creating a TCP connection. It’s used to bypass firewalls and your data won’t be intercepted, not even by the proxy server. So since SOCKS supports more applications than HTTP, it’s considered more secure than HTTP proxy.
SOCKS5 gives you even better layers of security making it ideal to use, but since most bots don’t support SOCKS proxies, you can only use it with a bot that supports it making its use limited.
Proxy Types Based on IP Origin
Depending on the IP source, proxies could either be residential as in from a real location, or data center as in from cloud service providers.
Residential Proxy
These are proxies based on real location. They are given by the ISP and the seller usually rents it out in exchange for other services such as BON service. They are slower than data center proxies but are used due to their availability and since they are less likely to be detected as a proxy when used.
Datacenter Proxy
These types of proxies are usually optimized with high bandwidth to provide the user with good speed and high performance. They are not associated with any ISP but come from servers that deal with proxies. Data center proxies are suitable for most web activities especially those involving bot use as they are fast and reliable.
Proxy Types Based on Anonymity Levels
The modifications of the HTTP header packets determine the levels of anonymity a proxy server provides. REMOTE_ADDR is usually added by the browser, but there are other headers that the proxy server can add.
Some headers used by the proxy server to show that a proxy is involved include:
HTTP_FORWARDED
HTTP_X_FORWARDED_FOR (XFF)
HTTP_VIA
Generally, the HTTP_VIA header provides details on the use of a proxy server. HTTP_X_FORWARDED_FOR header provides the IP address of the user. Even though the X_FORWARDED_FOR isn’t a standard header, it's used in combination by proxy servers with a standardized header.
1 . TRANSPARENT PROXY
Transparent proxies are also called intercepting proxy or forced proxy. Unlike what you know about proxies, transparent proxies do not modify your requests to a target website, so your IP address can be read. Since the proxy doesn’t modify the HTTP header and provides you with no anonymity level whatsoever, the webserver doesn’t detect it as a proxy.
The REMOTE_ADDR header is present which bears your IP address, so the sites you visit can recognize you. obviously, the purpose of this proxy isn’t anonymity and depending on its use, there are three types of Transparent proxy:
Interesting Read : Differences between http proxy vs socks proxy
Gateway Proxies: gateway proxies are a type of transparent proxies that are used in public Wi-Fi hotspots to restrict access to only those with permission. Whenever you try to log into a public Wi-Fi and you are redirected to a login page, it’s the gateway proxy at work.
Caching Proxies: this type of transparent proxy caches content on the server to facilitate quick delivery. Most content delivery networks use caching proxies to reduce loading time and enhance faster connections. ISPs also use this proxy to limit the bandwidth users consume.
Filtering Proxies: filtering proxies are used in workplaces and schools to prevent employees and students from accessing social media platforms for example, with the office or school network. Just as with other transparent proxies, the transferred data is not modified, and the administrator can eavesdrop on whatever data you share.
2. ANONYMOUS PROXY
An anonymous proxy is a type of HTTP proxies that hides your IP address by modifying the header so that the webserver has no idea who you are. The target website can detect the use of a proxy, but cannot tell who you are since the HTTP-X-FORWARDED-FOR header is modified, and the HTTP_VIA header is present. This proxy gives the least anonymity level and can be used with any protocol.
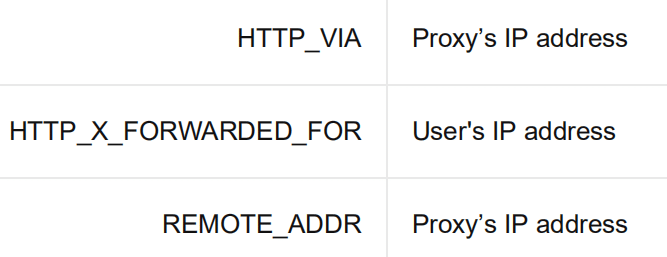
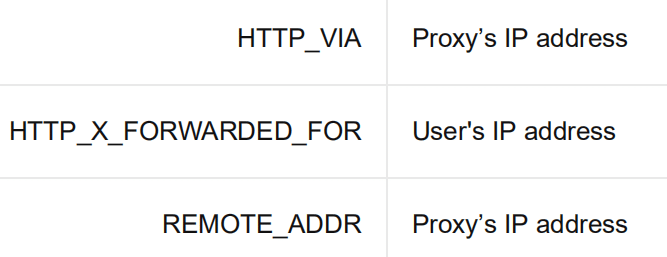
Anonymous proxies change the HTTP header information as the request is sent and the resulting HTTP header has two header comments: HTTP_VIA and HTTP_X_FORWARDED_FOR headers added to the REMOTE_ADDR header that’s already existing. The REMOTE_ADDR proxy is however replaced with the IP address of the proxy server and the HTTP_VIA header includes the IP address of the server. Since the X_FORWARDED_FOR header still contains the real IP address, the target website can still get the information, meaning your anonymity level isn’t solid.
It's up to the proxy server to include the X-FORWARDED-FOR header, and so for the sake of better anonymity, some proxy services overwrite this with their IP addresses, while others don’t include it at all. Doing this makes it more difficult to trace back a request to the client.
3. ELITE ANONYMOUS PROXY
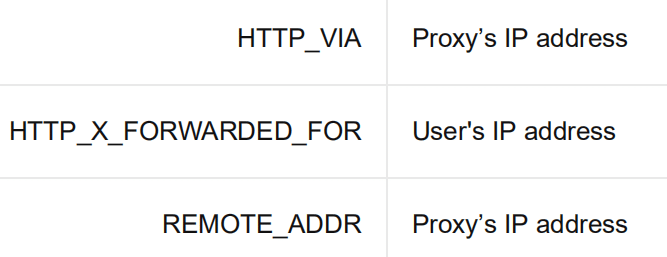
Elite Anonymous Proxy is similar to Anonymous Proxy but is even safer since this proxy gives you the highest anonymity level among HTTP proxies. It completely alters the HTTP header, removing any information and doesn’t include any forwarding commands. By this, the target website doesn’t see the request as coming from a proxy and treats it as a normal connection.
If you are looking to use HTTP proxies for web scraping and sneakers copping, Elite Anonymous Proxy is your best choice as the chances of your IP getting banned is slim since the webserver doesn’t see the connection as coming from a proxy.

About the author
Rachael Chapman
A Complete Gamer and a Tech Geek. Brings out all her thoughts and Love in Writing Techie Blogs.
Related Articles
How to Fight Ad Fraud in Digital Advertising?
Fraudsters see a world of opportunities from which to make money in digital advertising. Know how to Fight Ad Fraud in Digital Advertising
THE BEST INSTAGRAM BOTS OF 2020
Instagram is one medium that is growing and will continue to grow and if you aren’t active much on it. Here are the Best Instagram Bots for 2020